The Definitive Guide to Risk Management Enterprise
Wiki Article
All about Risk Management Enterprise
Table of Contents4 Easy Facts About Risk Management Enterprise ShownThe Greatest Guide To Risk Management EnterpriseGetting The Risk Management Enterprise To WorkRisk Management Enterprise Can Be Fun For AnyoneThe 20-Second Trick For Risk Management EnterpriseUnknown Facts About Risk Management EnterpriseThe Ultimate Guide To Risk Management Enterprise
Real-Time Risk Evaluations and Mitigation in this software application allow companies to continually keep track of and evaluate dangers as they advance. As soon as threats are determined, the software application facilitates instant reduction activities.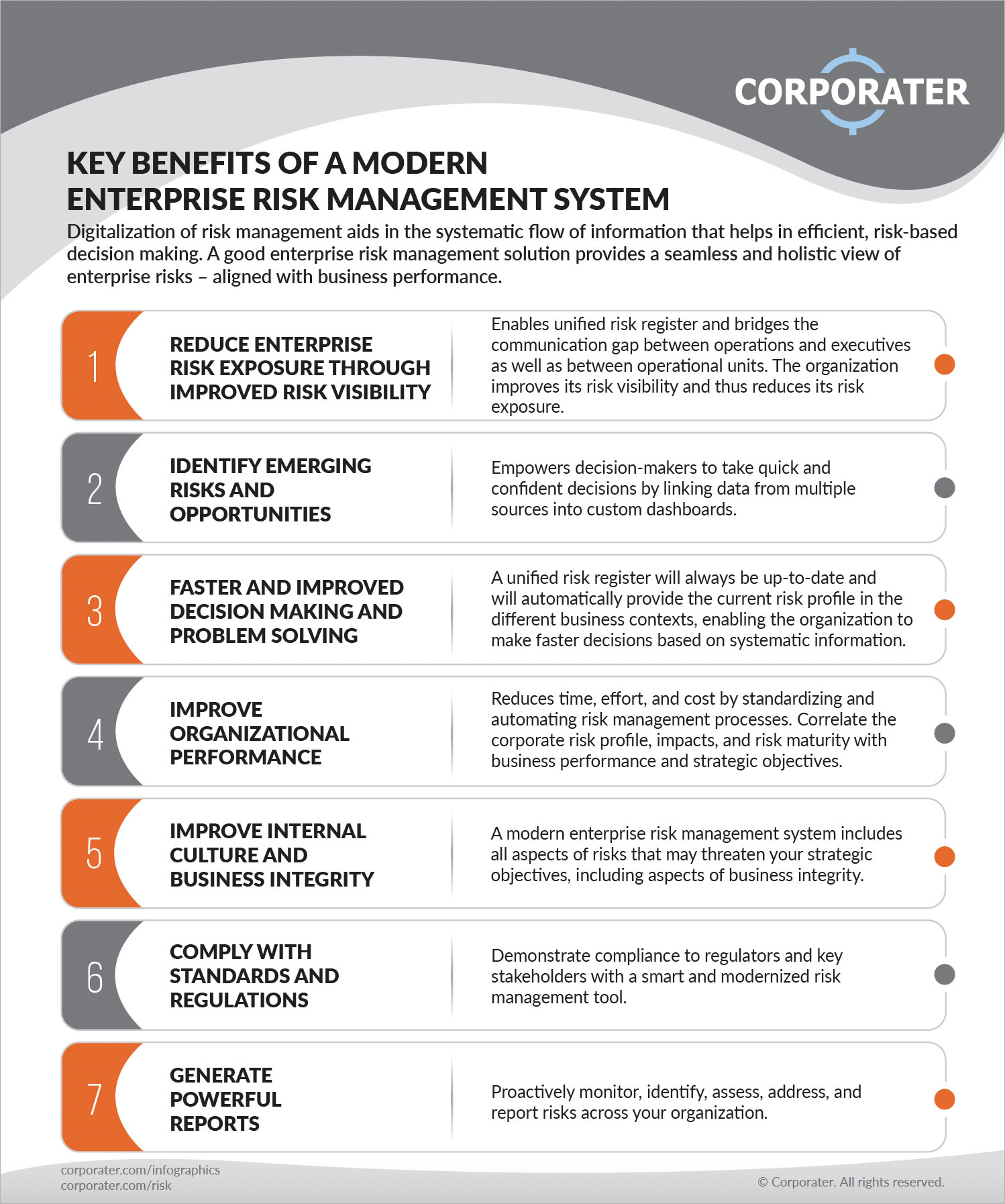
They resolve the obstacle of continuous risk monitoring by offering devices to monitor dangers continuously. KRIs improve safety and security danger oversight, making sure that potential threats are recognized and taken care of effectively.
The 7-Second Trick For Risk Management Enterprise
IT risk monitoring is a subset of venture risk administration (ERM), designed to bring IT risk in accordance with a company's danger cravings. IT run the risk of administration (ITRM) encompasses the plans, treatments and technology necessary to decrease threats and vulnerabilities, while keeping conformity with applicable regulatory demands. In enhancement, ITRM seeks to limit the repercussions of harmful events, such as protection violations.While ITRM structures offer helpful advice, it's easy for IT groups to experience from "structure overload." Veronica Rose, ISACA board director and a details systems auditor at Metropol Corp. Ltd., advises making use of a combination of frameworks to accomplish the best results. As an example, the ISACA Threat IT structure straightens well with the COBIT 2019 framework, Rose claimed.
Venture Risk Management Software Development: Perks & Qualities, Cost. With technological innovations, risks are constantly on the surge., businesses browse with a frequently changing sea of threats.
Risk Management Enterprise Can Be Fun For Anyone
In this blog, we will dive into the globe of ERM software, exploring what it is, its advantages, functions, and so on to make sure that you can build one for your company. Enterprise Danger Management (ERM) software application is the application program for preparation, guiding, organizing, and controlling service activities and simplifying threat monitoring procedures.With ERM, organizations can make informative decisions to enhance the general durability of the business. Committed ERM systems are important for services that routinely deal with vast amounts of delicate information and multiple stakeholders to accept strategic choices.
: It is difficult for any type of enterprise to undertake a thorough audit. It can be stayed clear of by using the ERM software program system. This system automates law compliance management to maintain the organization protected and certified. Aside from that, it likewise logs and categorizes all the documents in the system making it less complicated for auditors to examine procedures a lot quicker.
The 9-Second Trick For Risk Management Enterprise
You can also attach existing software systems to the ERM by means of APIs or by adding information manually. Businesses can use ERM to review dangers based upon their possible effect for much better threat management and mitigation.: Including this feature permits users to get real-time notices on their gadgets concerning any risk that may occur and its effect.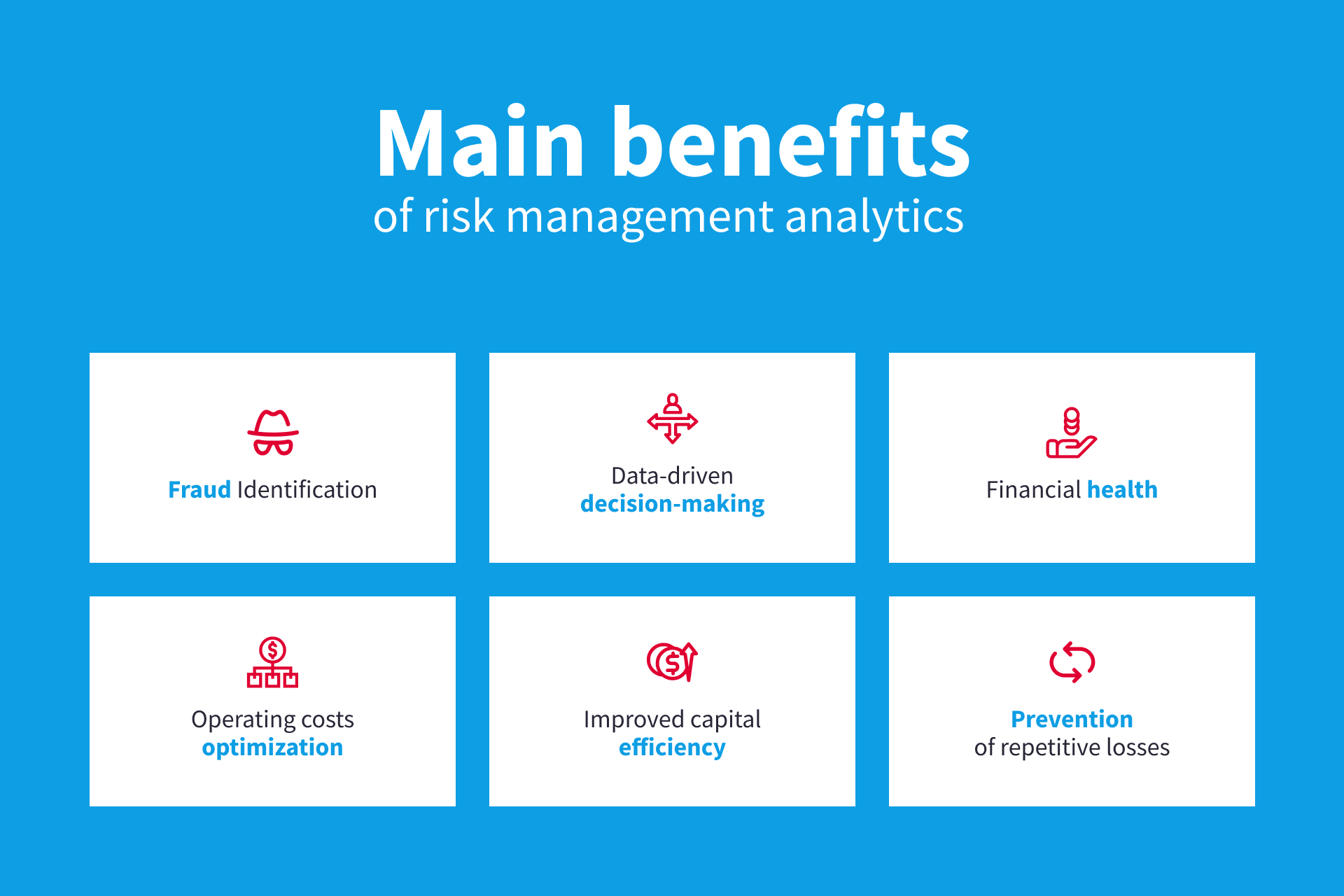
Instead, the software application allows them to set limits for various processes and send out push notices in case of feasible threats.: By integrating this article data visualization and reporting in the personalized ERM software, services can get clear insights about threat patterns and performance.: It is required for companies to comply with industry compliance and governing requirements.

These systems enable firms to implement best-practice risk monitoring procedures that line up with sector standards, offering a powerful, technology-driven technique to recognizing, analyzing, and mitigating risks. This blog checks out the advantages of automatic danger management tools, the areas of risk monitoring they can automate, and the value they give a company.
The Best Strategy To Use For Risk Management Enterprise
Teams can establish kinds with the pertinent areas and easily produce different forms for different risk kinds. These threat analysis kinds can be flowed for conclusion via automated operations that send notices to the pertinent personnel to complete the kinds online. If kinds are not completed by the deadline, then chaser e-mails are immediately sent by the system.The control monitoring and control testing process can additionally be automated. Companies can use automated operations to send out normal control examination notifications and personnel can enter the results using on the internet types. Controls can also be monitored by the software by setting guidelines to send alerts based upon control data held in other systems and spreadsheets that is pulled into the system through API assimilations.
Danger monitoring automation software program can additionally sustain with risk coverage for all degrees of the enterprise. Leaders can check out reports on risk exposure and control efficiency through a variety of reporting outcomes consisting of fixed records, Power BI interactive records, bowtie analysis, and Monte Carlo simulations. The capability to draw live records at the touch of a button removes strenuous data control jobs leaving threat teams with even more time to examine the information and advise business on the very best training course of activity.
The need for efficient has actually never been much more important. Risk Management site web Enterprise. Organizations operating in competitive, fast-changing markets can't pay for hold-ups or ineffectiveness in resolving possible risks. Standard threat monitoring making use of manual spreadsheet-based processes, while familiar, usually cause fragmented information, lengthy coverage, and a boosted probability of human error. Automating the danger monitoring process with software application addresses these shortcomings.
Unknown Facts About Risk Management Enterprise
This makes certain danger registers are always present and straightened with organizational goals. Conformity is another vital motorist for automating threat monitoring. Standards like ISO 31000, CPS 230 and COSO all supply guidance around danger management finest practices and control structures, and automated risk monitoring tools are structured to align with these needs assisting firms to satisfy most commonly utilized threat administration criteria.Try to find threat software application platforms with an approvals hierarchy to easily set up process for threat escalation. This capability enables you to tailor the sight for every customer, so they just see the information relevant to them. Ensure the ERM software application supplies individual monitoring so you can see who entered what data and when.
Look for out tools that use job threat management capabilities to manage your tasks and portfolios and the associated risks. The benefits of adopting danger administration automation software extend far past efficiency.

Risk Management Enterprise - The Facts
While the instance for automation is compelling, implementing a risk management platform is not without its obstacles. To get rid of the challenges of danger administration automation, like this companies should spend in information cleansing and administration to ensure a strong foundation for applying an automated system.Automation in risk management equips organizations to transform their technique to risk and develop a more powerful foundation for the future (Risk Management Enterprise). The concern is no more whether to automate danger administration, it's just how soon you can start. To see the Riskonnect at work,
The solution typically lies in how well dangers are prepared for and taken care of. Task monitoring software program acts as the navigator in the troubled waters of task implementation, offering devices that identify and analyze threats and devise techniques to minimize them successfully. From real-time information analytics to extensive danger surveillance control panels, these tools give a 360-degree sight of the job landscape, making it possible for project managers to make enlightened decisions that keep their projects on the right track and within spending plan.
Report this wiki page